Most of the Healthcare organizations now have mobile apps for their users. The apps are useful, interactive and make the life of their users simpler. Exchange of data is instantaneous and both the organizations and users are satisfied with the technology that equips them with handy mobile apps. But is everything as hunky-dory as it seems? Is everything well with the mobile apps of Healthcare organizations?
The perception is positive but the reality is apparently something very different, and to be honest, very alarming. Arxan technologies, an American company that specializes in providing anti-tamper protection for software, conducted a study and the results confirmed the fears of experts – Mobile applications of Healthcare organizations were not safe.
Study: The Perception
In November 2015, a third-party independent research organization analyzed a total of 71 popular mobile health apps from US, UK, Germany, and Japan. The apps selected were the most popular health apps of Android and iOS platforms from each region. 19 mobile health apps approved by US Food and Drug Administration (FDA) and 15 mobile health apps approved by the UK National Health Service (NHS) were included in the 71 apps.
The study brought out the glaring differences between the perceptions and the reality. Let’s look at some of the perceptions.
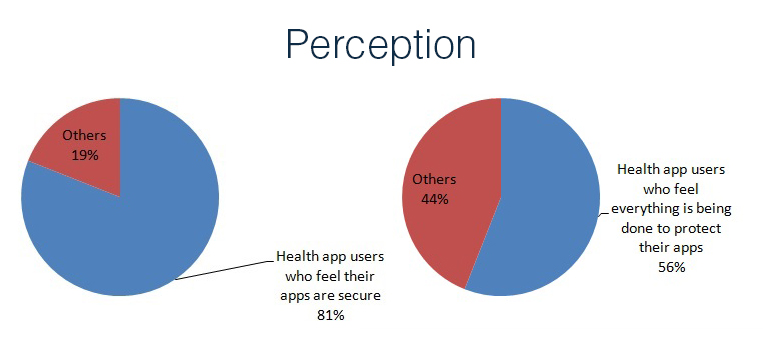
Users of these mobile health apps and the IT decision makers who have insight into the security of the mobile healthcare apps they produce or help produce and market feel it is safe. In fact to be accurate, 81% of them felt that their health apps were safe and their data and privacy was secure. About 56% of them were very confident of the Healthcare organization that provided the apps and of the regulatory authorities. They felt that the healthcare organizations were taking all the steps they could, to ensure the health apps remained safe from hackers and other technical vulnerabilities. The reality, however, is different.
Findings: The Reality
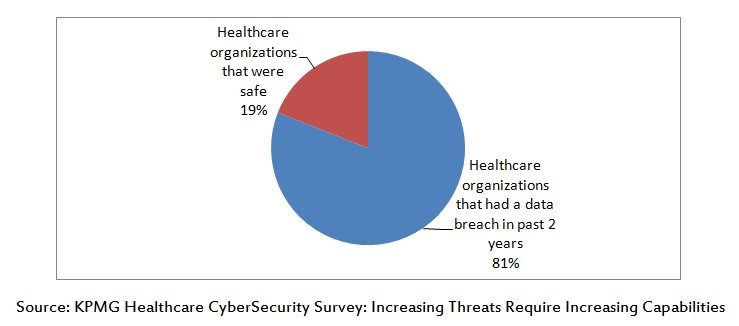
The study found out that about 81% of healthcare organizations had a data breach in past 2 years. The fact remains that a complete medical record of a person can fetch about $500 in the underground market. It makes hacking the medical data of a person a lucrative business for hackers. The data could be shocking for a few. There were more revelations from other studies.
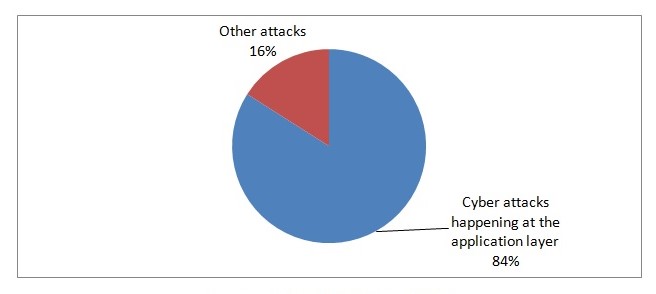
A study by Forbes/SAP also suggested that out of all the attacks that happened on a Healthcare organization, about 84% of them happen at the application layer. It means the apps of the healthcare organizations were the riskiest. They were being attacked for data by the hackers.
What are the organizations doing to counter such attacks? The revelations did not help.
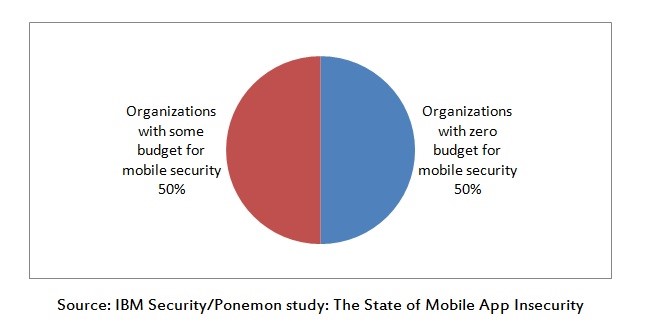
According to IBM Security study, about 50% of organizations in almost all the industries have zero budgets for mobile security. Healthcare industry has the same numbers. Almost half of the healthcare providers are either ignorant or too lazy to do anything about the threat of hacking via mobiles and apps. It is a scary scenario.
According to the security report, most health apps have significant vulnerabilities.
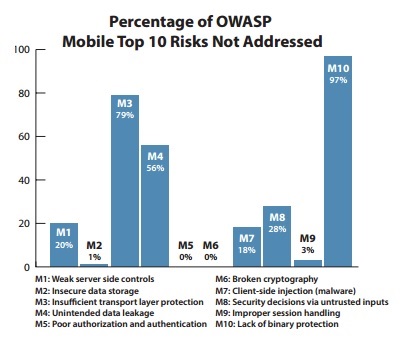
All the 71 mobile health apps collected from US, UK, Germany, and Japan went through vulnerability assessments. The vulnerability assessments conducted on the apps were based on OWASP (Open Web Application Security Project) Top 10 mobile Risks.
84% of the apps that were approved by the US Food and Drug Administration (FDA) did not adequately address at least two of the OWASP Mobile Top 10 risks. 80% of the apps approved by NHS (UK National Health Service) when tested, did not address at least two of the OWASP Mobile Top 10 risks.
97% of those 71 apps were vulnerable due to lack of binary protection. It means about 68 to 69 apps were vulnerable for M10 risk. About 79% of the apps suffered from M3 risk – which is due to insufficient transport layer protection. It means about 56 of the healthcare apps out of 71 suffered from M3 risk. All 71 of them were safe from M5 and M6 risks which were related to poor authorization and authentication and broken cryptography respectively. 86% of those 71 apps tested had at least two critical security vulnerabilities – it means, out of 71, 61 apps raised very serious concerns that needed immediate addressal.
Are users worried? If they knew the details, they would be. About 80% of the health app users claimed they would change their health care provider if the app they used from the provider had security risks or was vulnerable to attacks from hackers. They want their medical records and medical data to be safe.
So why are healthcare providers toying with the sensitive data of their users? Why aren’t they taking sufficient steps to curb the risks? What are the things they can do to safeguard their data? Let’s find out.
Related: Your Mobile Device Could Have Major Security Holes.
Recommendations to Curb the Risks
The study put forward a few recommendations.
- Security bar should be above regulations: Approval by FDA and NHS means nothing if they don’t address the security concerns of the apps. Regulatory bodies should pay attention to security concerns and address them with urgency.
- Take care of the major concerns: According to the study 97% of health apps that were tested, lacked binary code. 79% of the health apps had transport layer vulnerability. These obvious and glaring concerns should be addressed.
- Security can be the USP - Unique Selling Proposition: Healthcare organizations should make sure their apps are safe and they should then market this attribute to their users. It will definitely improve their bottom lines. Users do not opt for healthcare providers who cannot keep their data safe.

- Spend where the Risk is: According to IBM Security/Ponemon research most of the cyber attacks are happening at the application layer. Organizations don’t seem to realize it. Most of their data security spend is invested in protecting the network layer.
- Don’t root the devices: The consumers should get the apps from authorized app stores and they should not jailbreak or root the devices. It would help if they were more aware and asked for more transparency regarding the security of the apps. Ask for security certifications.
The Wrap
Security of app user’s medical data thus should be of paramount importance. The study showed little geographical discrepancies across US, UK, Germany, and Japan. Interestingly when the comparison was between iOS apps and Android apps, the iOS apps proved to be more vulnerable in this study. Here’s hoping that the healthcare organizations learn from this study and upgrade the security of their apps, in the interest of their users and in the interest of their businesses. There are a few lessons here for the app developers who develop the apps for the healthcare organizations too - beef up the security and mitigate the risks or your clients could lose out on business.







